How we set up Okta as an Altinity.Cloud® Identity Provider using Auth0

Altinity.Cloud provides automation to run and monitor Clickhouse environments. Altinity.Cloud users can initiate actions like starting, configuring or stopping clusters with only a few clicks or easily access critical database performance data. This means, our customers need to pay constant attention about how they distribute access within their organization.
Keeping access up to date on multiple platforms can become a tedious task. This is the reason some of our customers use Okta, an identity management platform. It enables them to keep their users synchronized on all systems to which it is connected. All our customers need to do is provide their Okta App integration credentials as described in Part 1 of this guide.
Okta integration is so simple for users that there’s not much more to say. It’s much more interesting to talk about how we implemented it. This blog article shows the path we took. We hope it is useful to other developers working on the same problem!
Background
Before starting to integrate Okta, Altinity.Cloud had already used Auth0 as an authentication platform, and there were no plans to change that. This meant we needed to add Okta as an Identity Provider to our Auth0 app. As easy as it might seem, there was no clear instruction on how to achieve this, with the only available articles on the topic being outdated, or describing reaching a different result (e.g. adding Auth0 as IDP to Okta).
The path we followed
It took us a few days to research the following process, which enables us to add any Okta account to our Auth0 authentication platform.
1. Set up Okta integration
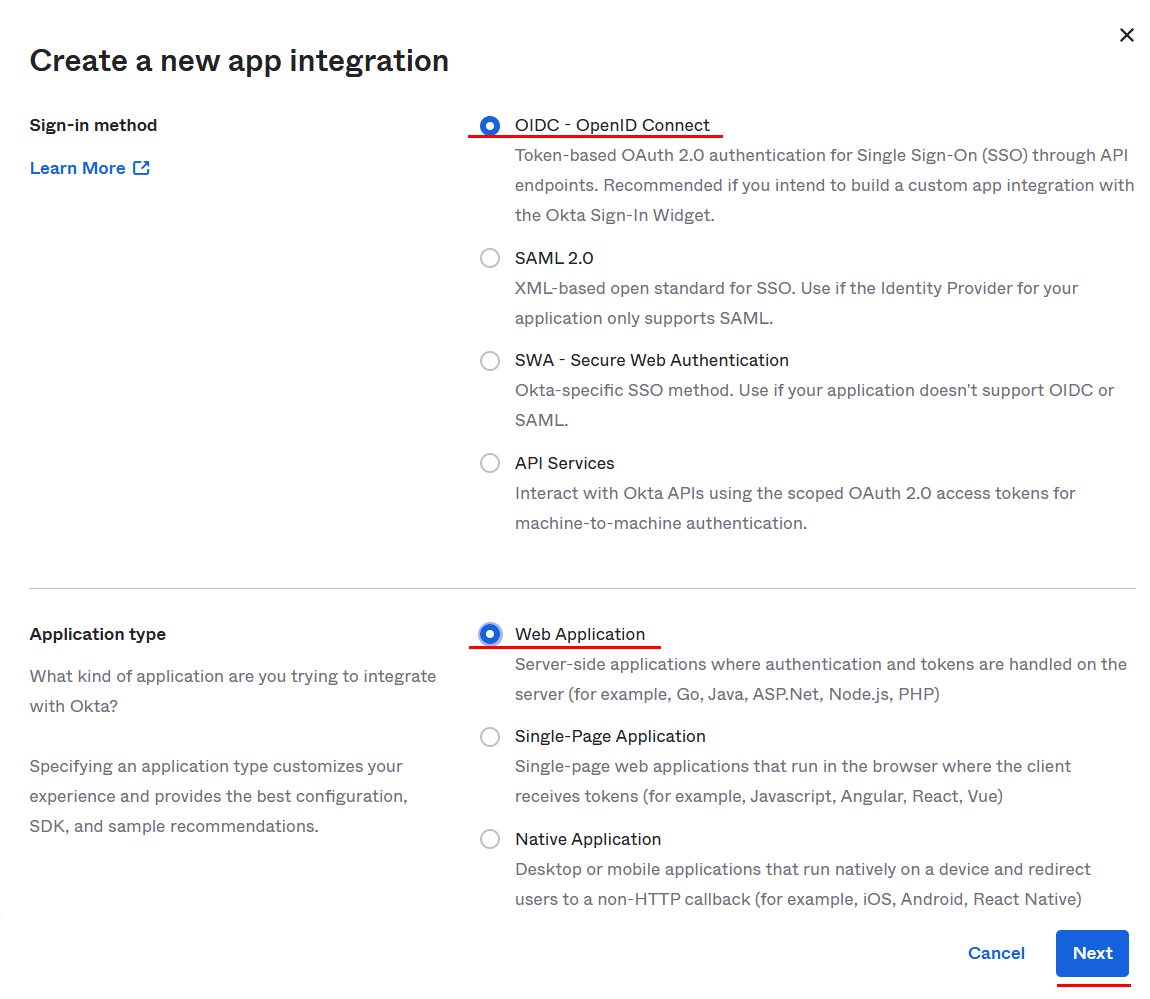
- Go to Okta Dashboard -> Applications -> Create App Integration

- Choose OIDC as Sign-in method and Web Application as Application type, then click Next

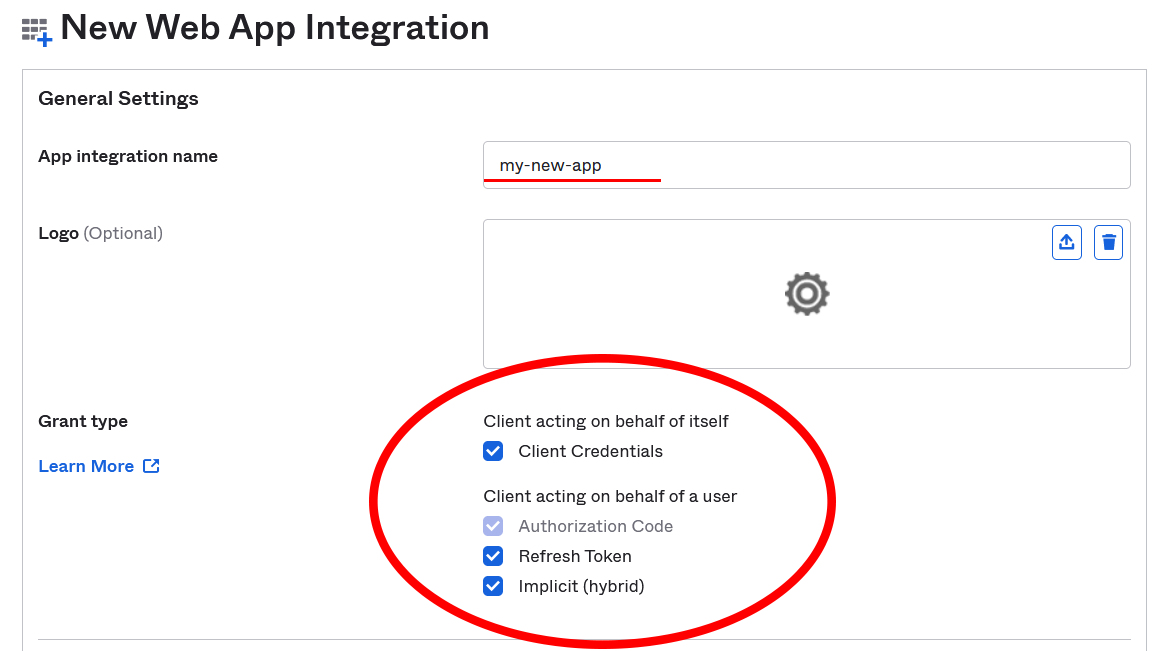
- Provide a name, and check all Grant type checkboxes

- Provide https://[YOUR AUTH0 TENANT NAME].auth0.com/login/callback as Sign-in redirect URI.

You can find your Auth0 tenant name in the upper left corner of your Auth0 dashboard.
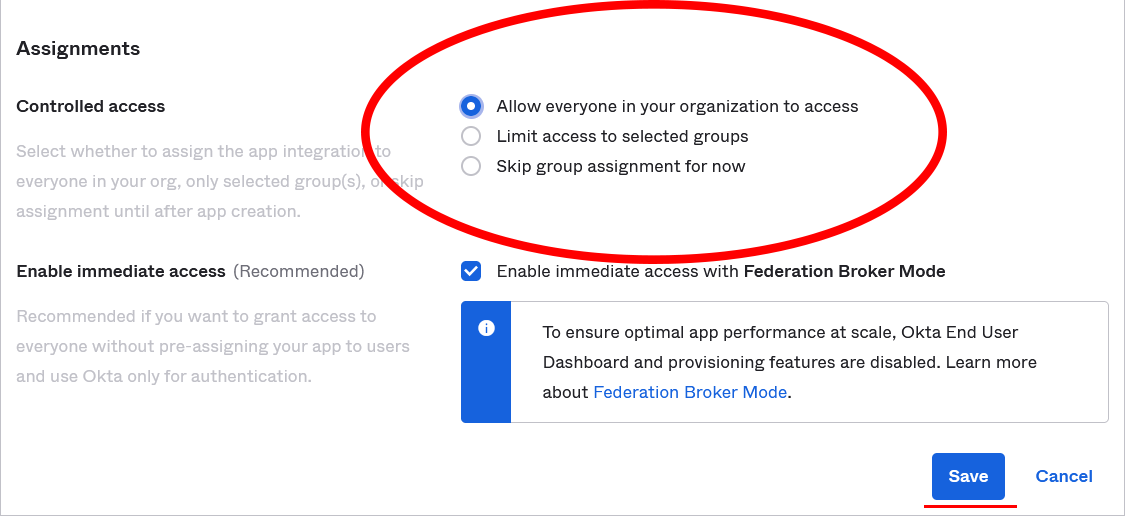
- Choose preferred option for Assignments. In this case, we have chosen to allow access for everyone in our organization.

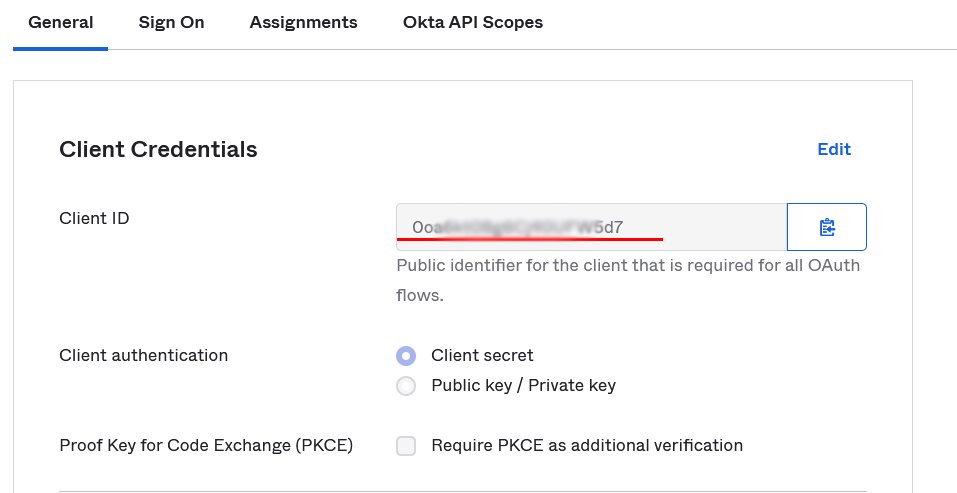
- Click Save and leave page open. You will need General -> Client Credentials -> Client ID. (If you closed the page, go to Dashboard -> Applications -> click on your application name.)

You will also need your Okta URL, found in the upper right corner of your Okta dashboard.
2. Set up Auth0 connection
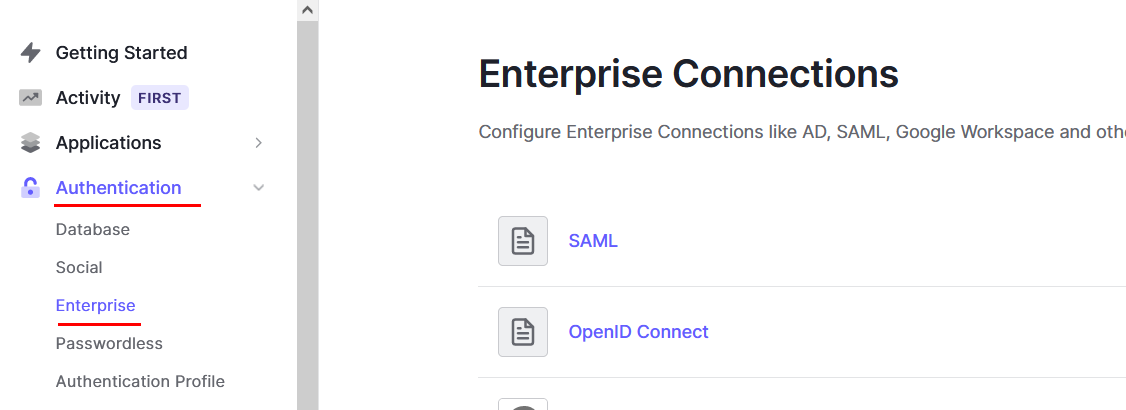
- Go to Auth0 Dashboard -> Authentication -> Enterprise

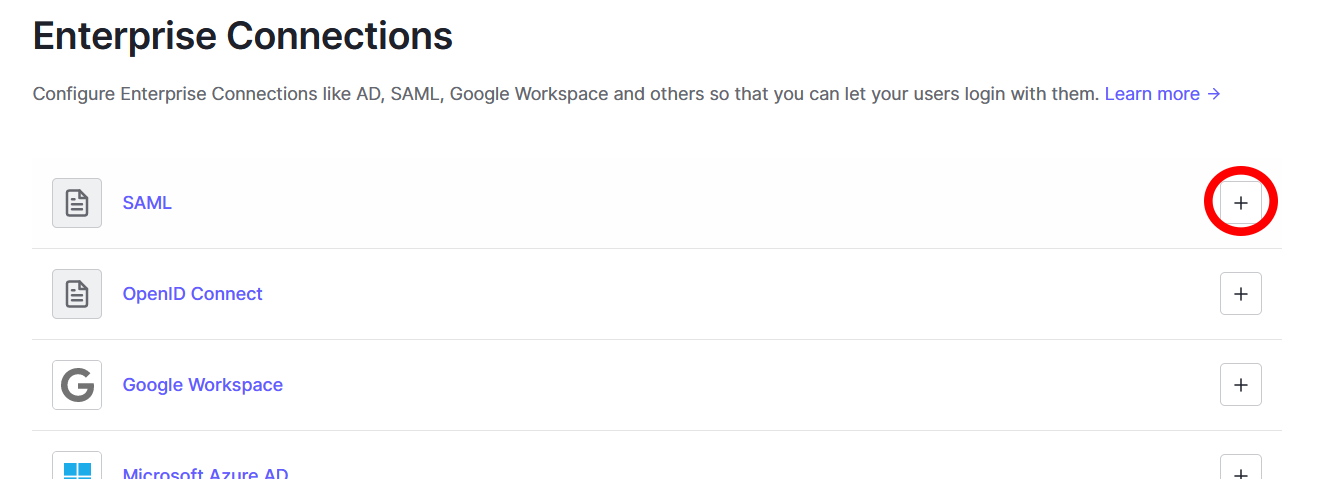
- Click Create (plus icon) next to OpenID Connect

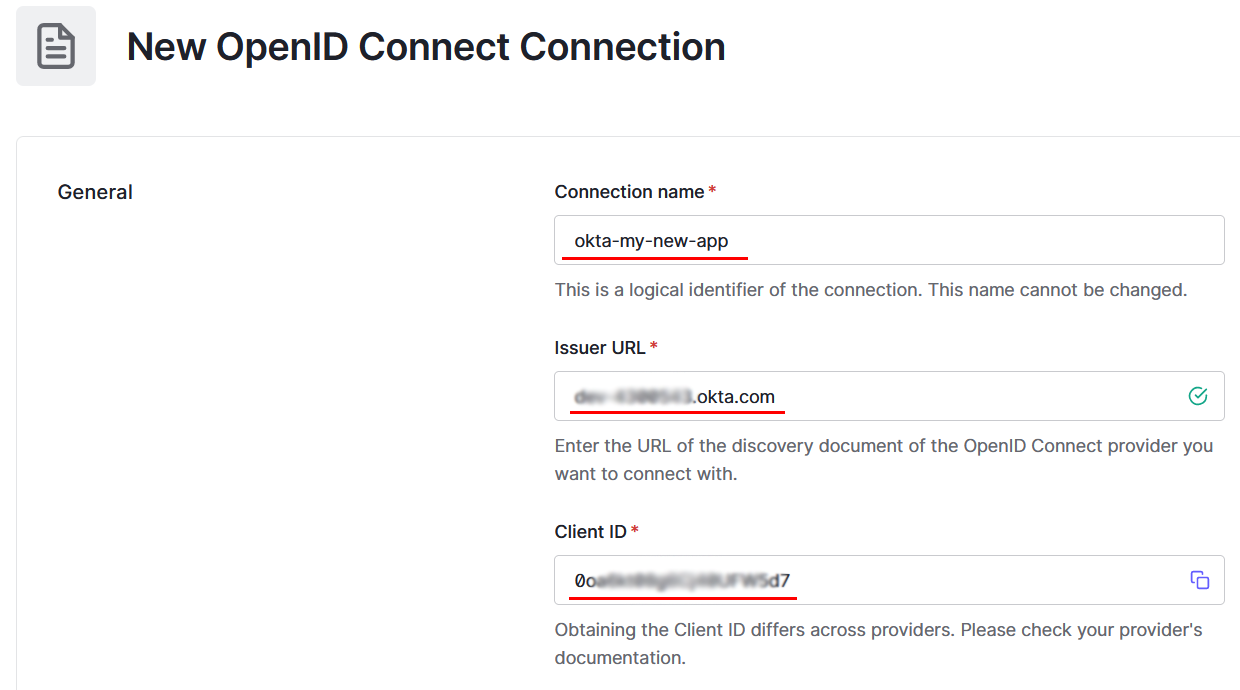
- Provide a name
- Copy Okta domain from step 1.6. to Issuer URL
- Copy Client ID from step 1.6. to Client ID

- Click Create at the bottom of the page
3. Enable connection
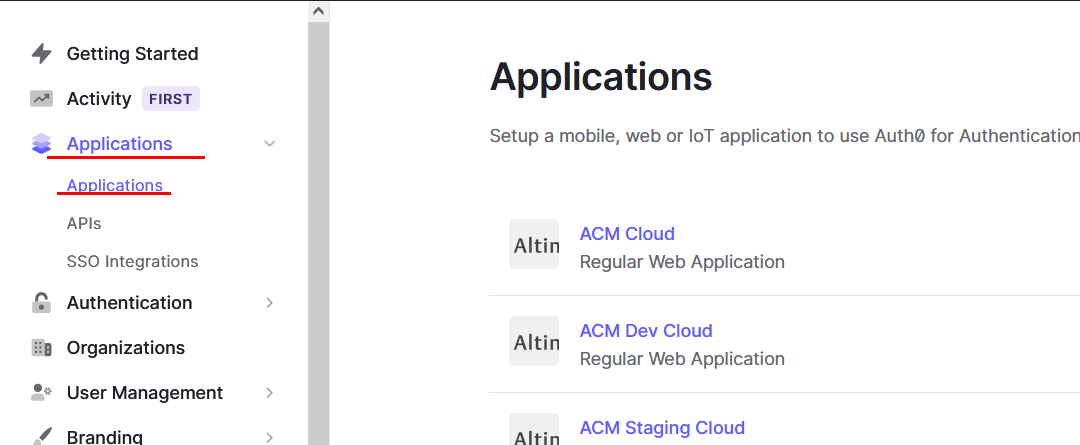
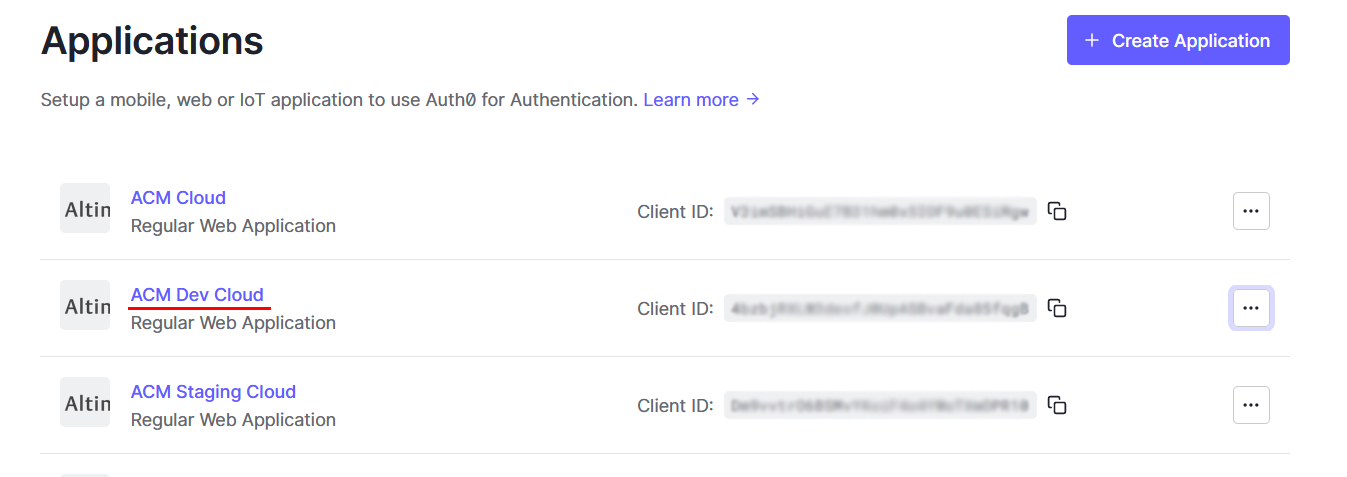
- Go to Auth0 Dashboard -> Applications

- Click the application you wish to use with the connection

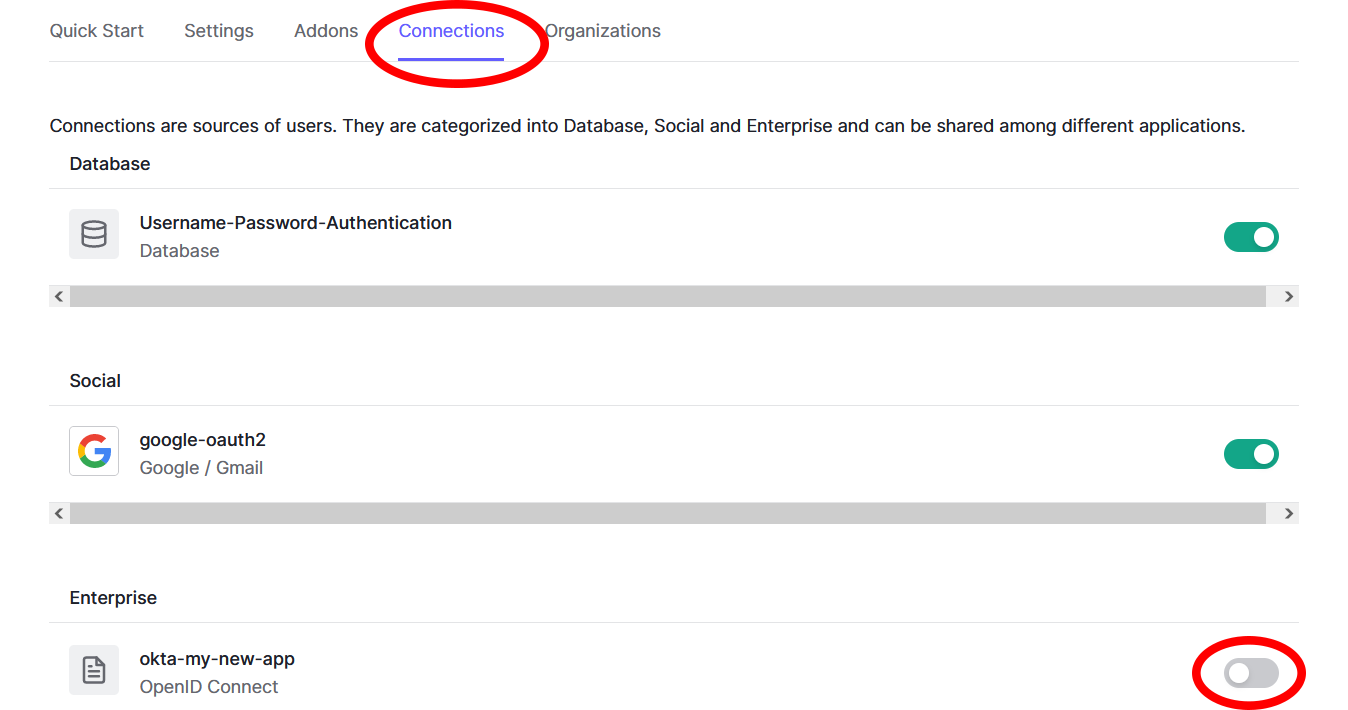
- Go to Connections tab, find your newly created connection and switch it on

4. Test connection
- Go to Auth0 Dashboard -> Authentication -> Enterprise

- Click OpenID Connect (the text, not the plus sign)

- Find the newly created connection
- Click the three dots on the right -> Try

- You should be greeted with an Okta password prompt, or if there is a problem, an error is shown
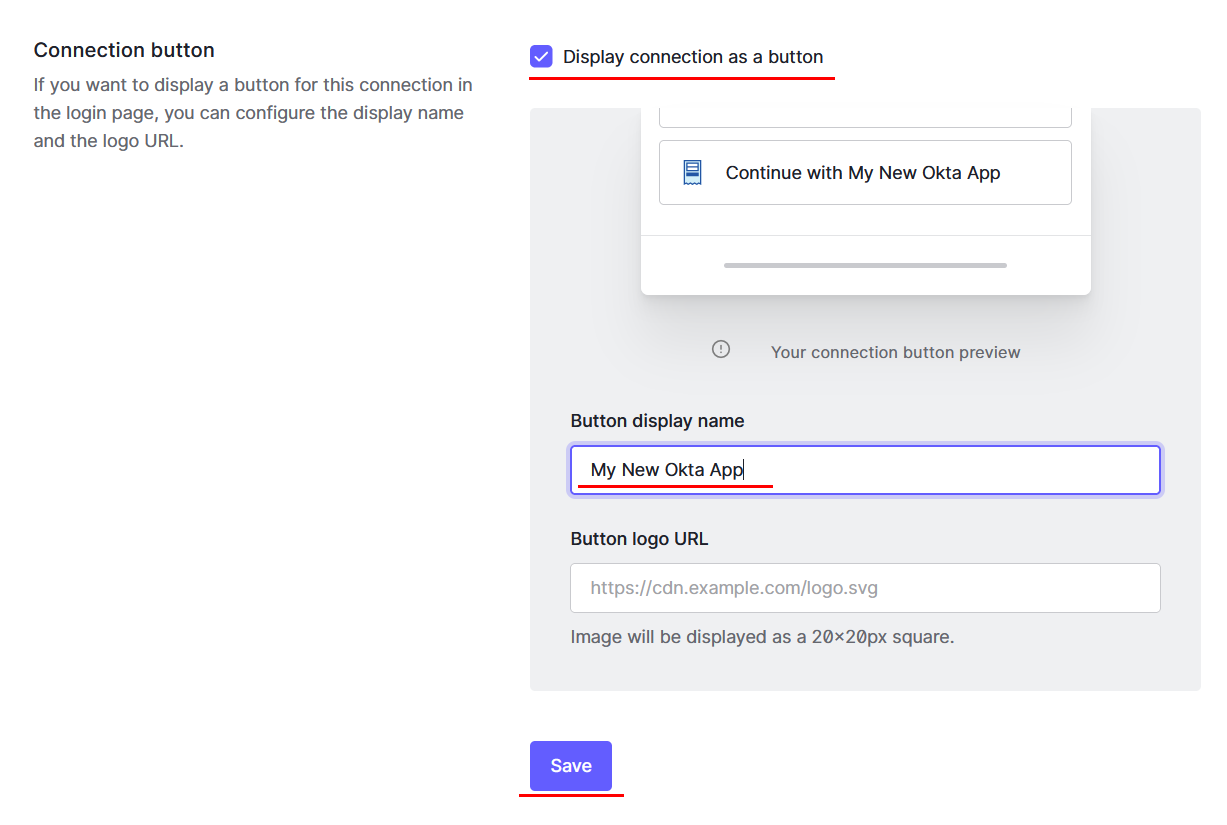
5. Enable button
- Go to Auth0 Dashboard -> Authentication -> Enterprise

- Click OpenID Connect (the text, not the plus sign)

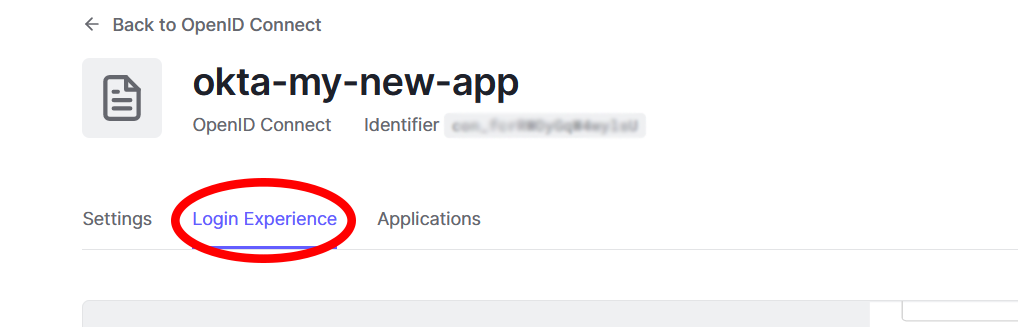
- Find the newly created connection and click its name

- Go to Login Experience tab

- Check Connection button -> Display connection as a button
- Configure Button display name and logo URL
- Click Save

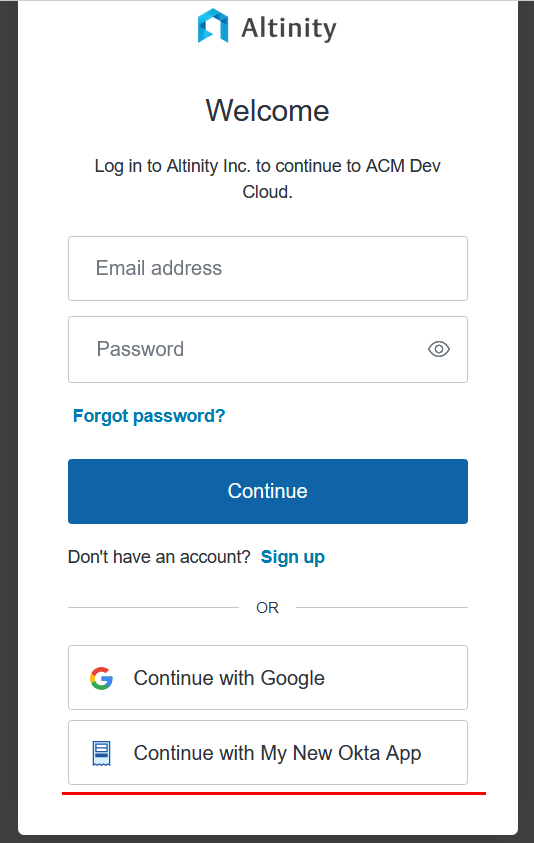
6. Final test
- Go to your application’s login page and try to log in with Auth0
- A button for the new connection should be shown

- On clicking the button, Okta should either ask for login credentials or log straight into the app (depending on being logged into Okta already)
Notes on testing and going live
If you followed through Part 6 of the guide and were able to log in, congratulations, you have successfully completed and tested integrating Okta!
This might be self-explanatory for developers who are more experienced with a platform like Okta or Auth0, but don’t expect all of your users to show up in your application database instantly. It depends on how Auth0 is integrated with your application, with the most usual way being users registered on their first login.
If you have an application supporting multiple access levels, don’t forget that you might still need to set them up manually for your new users inside your application, and make sure to assign the lowest access to new users by default. Or, as a more advanced and automated solution, you can query user properties (e.g. groups) in Okta and use it as a source for the user’s permissions in your app, developing a truly centralized access management system. If you prefer to manage access within your app, it is also possible to modify Okta users via API. Just make sure it doesn’t interfere with other applications connected to Okta.
Final remarks
Both Auth0 and Okta tend to change their user interface, so it is possible that by the time of reading this, some of the steps will be outdated. Please let us know if this happens, so we can update this guide accordingly.
Also, if you or your company works with Clickhouse or plans to use Clickhouse for marketing analytics in the future, do not forget to check out Altinity.Cloud. On top of making your database deployment and monitoring tasks a lot easier, our team can provide you with expert guidance from as early as the inception of your project, independent of your hosting platform.
To learn more about Altinity.Cloud, ClickHouse or Okta, please contact us or join our public Slack workspace. We have helped hundreds of companies to build better analytic applications on ClickHouse.
ClickHouse® is a registered trademark of ClickHouse, Inc.; Altinity is not affiliated with or associated with ClickHouse, Inc.